Table of Contents
Why 2026 Is the Year You Can’t Afford to Wait
It’s a threat that is right in your encrypted archives these minutes – and it does not have to do anything today.
The enemies will soon be reaping encrypted information in mass, retaining it latently, and biding their time. This strategy is called harvest now, decrypt later. Once a quantum computer capable of cryptanalytic significance is developed (concrete strength that can break RSA and elliptic curve cryptography) years of intercepted data can be decrypted overnight.
Organisations are confronted with classified records, monetary dealings, enduring identity releases, and confidential communications that they had thought were safely secured on an encrypted database are suddenly turned upside down.
The painful reality is that the quantum is still years off is no excuse to postpone. When your organisation has a confidentiality requirement of five years or above on the data it deals with that data is already compromised today, as the harvest has already gotten underway.
NIST realised this and acted expeditiously. It completed the first generation of post-quantum cryptographic standards, FIPS 203 204 and 205, in 2024, which provided the industry with an implementation of the first concrete and easily implementable algorithms. The said publication eliminated the final viable justification of having PQC listed under the watchlist column.
Governments are moving it now to hard time periods. The quantum-safe migration roadmap in Canada recommends the departmental migration plans to be in place by April 2026, the high-priority migration to system migrations to be finalized by 2031, and the final migration of the remaining systems to be complete by 2035.
The European Union, United States and others are moving at the same pace of converging into the same phasing schedule. Although your organisation may not have these particular jurisdictions, these timeframes of 5 to 10 years of migration are more or less universally agreed as the timeframe of realised large-scale cryptographical migrations.
2026 isn’t the deadline. It is the most realistic start position to win the deadline.
The Quantum Threat and PQC Basics – What Security Teams Actually Need to Know
Quantum computing subverts the public-key cryptography in a certain algorithmic attack. Short’s algorithm was executed on a quantum computer of high enough power to factor large integers and break discrete logarithm problems in a limited amount of time. That kills the mathematical basis of RSA, Diffie-Hellman and elliptic curve cryptography (ECC) – the keys to the encryption of most current encrypted communications, digital signatures and key exchanges.
Symmetric cryptography AES, e.g., is another thing. The algorithm proposed by Grover provides quantum computers with quadratic speed-up over symmetric ciphers, but the countermeasure is quite simple: to deny the algorithms their protection, one has to simply increase the key length (say, AES-128 to AES-256). No rearchitecting required.
The post-quantum cryptography addresses the problem of the key publicity by substituting RSA and ECC with an algorithm whose mathematical problem cannot be solved efficiently by quantum computers. The concluded standards of NIST provide two major families:
Key Encapsulation Mechanisms (KEM): Key exchange. The standardisation of ML-KEM (previously CRYSTALS-Kyber), a lattice-based scheme, which is the main alternative to classical key exchange protocols, is codified by FIPS 203.
Digital Signature Schemes: This is applied in authentication and integrity. The FIPS 204 standardises ML-dSA (CDIL to CRYSTALS) and the FIPS 205 standardises SLH-DSA (SPHINCS+). They displace RSA and ECDSA signature in code signing, certificate authority and authentication systems.
The operation of how these algorithms operate and in which applications best they apply is further divided in NIST Post-Quantum Standards Explained: KEMs and Signatures that article delves into the cryptographic properties, performance/cost consideration, and scenarios of application, of each standard.
Global Roadmaps and Deadlines Security Teams Should Map Against
The schemata are no longer existentialist. Concrete, as in phases of migration, have been published by various governments and standards organisations – and unorganised organisations who have not matched internal planning to external milestones are already falling behind.
One of the most elaborated public structures is the PQC Migration Roadmap of Canada. It establishes three specific milestones to be achieved by April 2026 and includes the initial departmental migration plans, the high-priority and high-impact systems to have been migrated by 2031, and the rest of the systems should have been migrated by 2035.
The architecture is based on the same staged reason advocated by the Post-Quantum Cryptography Coalition (PQCC) preparation, inventory, planning, execution and monitoring.
The United States National Cybersecurity Strategy and the CNSA 2.0 suite of NSA is placing pressure on national security systems and by 2025 software and firmware must be supported with PQC, and by 2030 and beyond, the network equipment and legacy systems must come on board. Migration guidance has been posted by NIST NCCoE in the form of NIST SP 1800-38 precisely in attempt to enable organisations to operationalise these transitions.
PQC transition was coordinated by the release of a implementation roadmap by the European Union and ENISA released a dedicated PQC integration study of the interaction between post-quantum standards and existing security frameworks in member states.
The common use of all these frameworks is the 5-10 years implementation plan whereby planning activities are packed up to 2025 and 2026 duration. Companies that use the end date (2031, 2035) as the planning date, instead of the execution date, will see themselves cramming years of intricate migration work through a diminishing time slot.
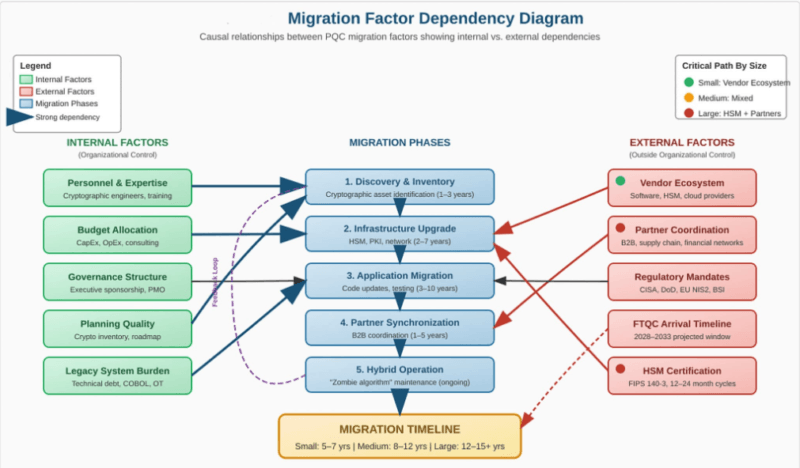
These timelines should constitute points of calibration even in organisations that are not within these three jurisdictions. The complexity of migration is an actual thing, the discovery stage is always underestimated and the dependency graphs within the current cryptographic infrastructure are even longer than most security teams had anticipated.
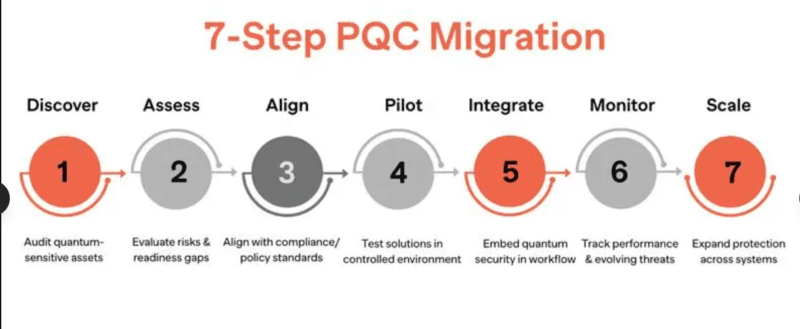
Your PQC Migration Phases – Aligned With Official Roadmaps
All four category roadmap of the PQCC and TNO PQC Migration Handbook and NIST NCCoE migration project are all coming to the identical high level phase architecture. The next thing is that structure organized into an operational framework.
Phase 1 – Preparation and Quantum-Vulnerability Diagnosis
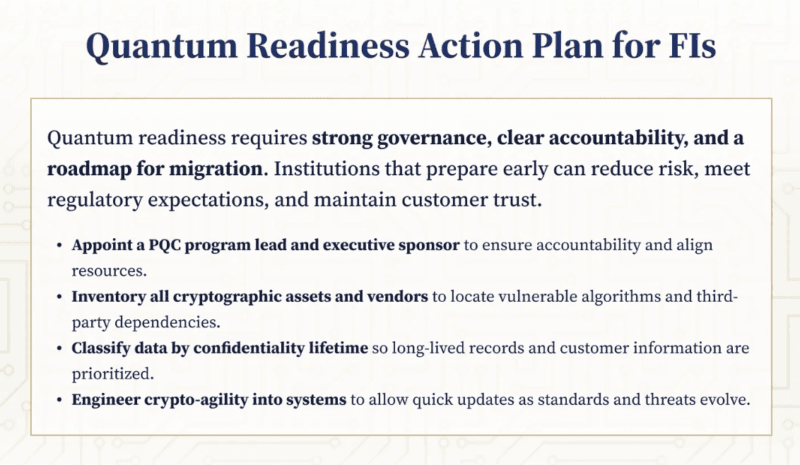
Organisations require a governing body prior to the commencement of technical work. This step is concerned with the building of the internal systems that will lead by the migration in terms of multi-year implementation.
Select a single migration head – owner of crypto or veteran security architect who can make decisions on behalf of faculties. Build the stakeholder group (security, compliance, legal, procurement, and business unit representatives) who own the systems where there is cryptographic relation in front of them. Determine the risk that the organisation is prepared to take regarding quantum exposure (that is, of sensitive data that lasts longer than a year).
Initial quantum-vulnerability diagnosis This stage also entails initial high-level determination of the type of systems that tend to have RSA or ECC dependencies prior to the beginning of the detailed inventory. The output does not deliver a list of all asset components, it is a knowledgeable scope statement, which influences the way that Phase 2 is resourced.
As a more comprehensive model of threat modelling including risk classification at this level, see Quantum Threat 101: Why RSA and ECC Won’t Last.
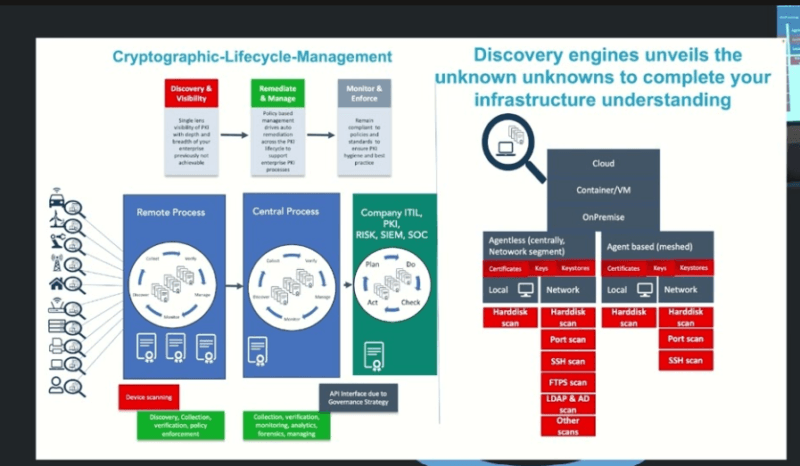
Phase 2 – Cryptographic Inventory and Baseline Understanding
This is where majority find that the migration is even bigger than expected. The cryptographic dependencies are distributed over a broader surface than security teams can typically monitor e.g. TLS configuration, certificate authority, code signing pipelines, SSH deployment, VPN infrastructure, database encryption layer, IoT and embedded systems, and third party software libraries.
The intent of such a phase is a Cryptographic Bill of Materials (CBOM) – a formal listing of all cryptographic assets, the algorithm that they employ, the key length, and the sensitivity designation of the data they are protecting. The CBOM then acts as the engine of prioritisation of the next phases.
There is discovery tooling, which I find always counts cryptographic usage in custom applications, and in legacy systems, generally undercounts cryptographic calls since they are generally not called on either of the standard libraries in most cases. Manual verification and interviews with developers are not some extra ingredients but the ones required to make it complete.
A more realistic approach to creating andupkeeping a CBOM is available at Cryptographic Inventory and Quantum-Vulnerability Diagnosis.
Phase 3 – Planning and Execution
Using a repository, the planning process then transforms the findings of discovery into a prioritised migration plan. The criteria of priority involve:
- Sensitivity and longevity (high-sensitivity data last) The first data type that comes to mind is sensitive in nature (high sensitivity) and long-lived.
- System urgency and exposure (high urgency by internet facing systems)
- Complexity of dependency (dependencies with many cryptographic dependencies take more time to lead time)
- Vendor and third party fitness (it is as fast and slow as the slowest dependency)
The group of pilot projects needs to target a representative high-priority system – one complicated enough to expose the issues in integration, but small enough to finish and test between specified intervals. Hybrid cryptographic configurations testable by pilots are immediate to run during transition on configurations with both classical and post-quantum algorithms running simultaneously.
The performance differences should be taken into consideration in the rollout planning. Classical schemes consume small overhead compared to lattice-based KEMs, however, signature algorithms such as SLH-DSA have larger key and signature space, and so impacts bandwidth-limited functions. It is not a choice to test under loads that represent production and then roll out.
Detailed execution structures including prioritisation methodology, vendor engagement and rollout order are outlined in Planning and Executing Your PQC Migration: From Pilots to Rollout.
Phase 4 – Monitoring, Crypto-Agility, and Continuous Alignment
Migration completion does not establish itself. The PQC topography will change – NIST has indicated that it is possible to standardise more algorithms and cryptanalysis against existing candidates is ongoing. Organisations that incorporate crypto-agility into their design early on the ability to transition cryptographic algorithms without having to redesign systems will be in a position to adapt to change in the future without the need to undertake the entire migration process again.
Monitoring tasks that may be focused on include: keep track of NIST and NCCoE guidance updates, keep track of the CBOM as systems are modified, keep track of vendor PQC roadmaps of dependencies that are not yet migrated and ensure that post-quantum configurations remain intact as systems are updated.
The 2026 Migration Checklist – What to Do This Year
The phase framework can be translated as specific 2026 actions as shown in the table below. These are the bare minimum steps one needs to have so that one can be in a credible migration position by the year end.
| Priority | Action | Owner | Output |
|---|---|---|---|
| 1 | Appoint PQC migration lead | CISO | Named owner with mandate |
| 2 | Establish steering group | Security + Compliance | Cross-functional team in place |
| 3 | Define scope — classify long-lived sensitive data | Crypto owner | Risk-stratified data map |
| 4 | Launch cryptographic discovery | Security architecture | Initial CBOM draft |
| 5 | Assess vendor PQC readiness | Procurement + Security | Vendor roadmap register |
| 6 | Identify pilot candidate system | Security architect | Pilot scope document |
| 7 | Review applicable regulatory timelines | Compliance lead | Jurisdiction gap analysis |
| 8 | Establish crypto-agility design principles | Architecture team | Design standards update |
The checklist above is merely a commencement of a programme plan rather than a comprehensive one. Everyone is connected with thorough execution work, the discovery work alone can take 6 to 12 months in a huge organisation. The difference between having a pilot in progress and in discovery at year-end is starting in Q 1 2026 as compared to Q 4 2026.
Common Pitfalls – What Early Adopters Learned the Hard Way
The TNO PQC Migration Handbook, as well as the PQCC guidance, are based on the initial organisational experiences of PQC transition. The trends, which form, are sufficiently similar to assume they are planning assumptions rather than edge cases.
Delaying in making a discovery. The cryptographic inventory stage is more expensive and lasts longer than virtually all organisations estimates. The applications that are written directly, legacy systems and the third party integrations always give rise to the cryptographic dependencies, which are not detected by automated scanning.
Looking through my experience with revising migration programmes at early stage, preliminary discovery estimates usually should be doubled to include manual scrutiny and developer interaction. Develop the schedule as a result.
Disregarding constrained machines. The IoT, operational technology, and embedded systems become a unique challenge. Large signature schemes post-quantum algorithms have the potential to outgrow the memory and processing capabilities of older equipment.
Those organisations that view constrained devices as an after-thought find themselves late into the deployment cycle to the realisation that a large part of their environment is in need of replacement hardware and not a software upgrade. These are to be identified in inventory stage and they need to be included in the budget and timeline planning.
Pushing flying crew without crypto-agility. Hard coded piloting of post-quantum algo options which are not designed to be agile in nature generates technical debt making subsequent transitions of the algorithm more difficult. The crypto-agility architecture cannot be omitted at the pilot, but it must be validated at the moment.
Complacing dependency on vendors. PQC migration relies on vendor coverage in all the levels of technology stack. The vendors do not all share their roadmap and some of the dependencies might not have a post-quantum upgrade path within a timeline that suits the organisational needs. PQC vendor preparation analysis ought not to be commenced in the year of rollout planning commencement, but in 2026.
Failure to factor in precedent of previous migrations. The withdrawal of SHA-1 had bedeviled the industry more than a decade even though it was a well-known, focused, and technically simpler move than the mass PQC decommissioning. The move to 1024-bit RSA also lagged several years behind estimated times.
PQC migration is the concept that seeks to substitute the basic cryptographic primitives on an immensely larger scale. It is reasonable to begin in 2026, with an anticipated completion date of 2031 or 2035. Starting in 2028 is not.
Technical advice on how to design hybrid constructions allowing the systems to act in classical and post-quantum mode switching between them can be found in Hybrid and Crypto-Agile Strategies: Migrating Without Breaking Everything.
Free Resources Worth Using and How to Leverage Them
The PQC migration research foundation is truly robust, and most of the finest articles are free to access.
Migration planning is primarily referred to by the SP 1800-38 by NIST NCCoE. It includes the methodology of discovery, the prioritisation of risks, and integration guidance. It is thick, and even the first drafts are already so detailed as to brief the programme planning. Consider the NCCoE migration content.
The main open-source project on an experimentation with post-quantum algorithms is Open Quantum Safe / liboqs. Evaluation of liboqs that I conducted revealed it to be a sound basis to study the nature of algorithm performances prior to carrying out production version. It assists with ML-KEM, ML-dSA as well as SLH-DSA and support experiment algorithms. On openquantumsafe.org.
The post-quantum TLS experiments at Cloudflare give real-life data of the hybrid TLS performance and compatibility with the public internet. Cloudflare has been operating post-quantum key exchange in production systems and reporting results – these can be useful metrics to organisations intending to deploy hybrid TLS. Their series of post quantum blogs should be read by engineering crews.
ENISA PQC Integration Study under consideration analysis of the interaction of post-quantum standards with the current EU frameworks on security would be beneficial to compliance leads operating with European regulations. Accessed on the ENISA publications page.
External Authoritative Related Links: Trust Boosters.
- NIST Post-Quantum Cryptography Standards (FIPS 203/204/205) – this is the main standards reference of any PQC programme. Anchor text: “Finalised standards of post-quantum cryptography of NIST.
- PQCA / Open Quantum Safe Project – the industry group which orchestrates open-source PQC tooling and open-source PQC adoption. Anchor text: Post- Quantum Cryptography Alliance and the Open Quantum safe project.
Who This Playbook Is For and the Honest Assessment
This guide is constructed to guide the people who need to construct the plan not to read about the threat. Boards that require to be briefed by CISOs. Security architects that must scope the migration programme. The owners of the CBOM will be crypto. The leaders of compliances will have to chart domestic timetables as compared to government standards.
The truth is told: The next stage of cryptographic transition of a scale is post-quantum migration, purportedly the most difficult undertaking the industry has ever ventured into. It has broader systems involvement, is more durable in dependency and therefore demands greater sustained organisation commitment than any other previous migration. SHA-1 depreciation was less complex and it was up to a decade. The necessary time will not be shorter because it is scheduled in a longer way on a paper.
The reason why 2026 is a plausible point with which to begin is that the standards are no longer in flux, that the guidance frameworks have been published, the open-source tooling is operational, and that the government timelines are tangible. One cannot believe that one has to wait till this becomes clear, but this clarity is there.
Start the inventory. Appoint the lead. Engage the vendors. The ones that achieve in 2031 milestones will then be the organisations that start structured migration programmes in 2026. Those that would wait out to 2028 will be to the regulatory people explaining why they did not.
The article is part of a group of papers describing the entire PQC migration lifecycle. Some of the following articles discuss Quantum Threat 101: Why RSA and ECC Won’t Last, NIST Post-Quantum Standards Explained: KEMs and Signatures, Cryptographic Inventory and Quantum-Vulnerability Diagnosis, Planning and Implementing Your PQC Migration: From Pilots to Rollout, and Hybrid and Crypto-Agile Strategies: Migrating Without Breaking Everything.
Read:
Identity Crisis – Securing Non-Human Identities for AI Agents
Data Privacy in AI-Powered Security Systems: Protecting Privacy While Detecting Threats
I’m a technology writer with a passion for AI and digital marketing. I create engaging and useful content that bridges the gap between complex technology concepts and digital technologies. My writing makes the process easy and curious. and encourage participation I continue to research innovation and technology. Let’s connect and talk technology!