A silent countdown is occurring to the background of all the encrypted connections you are making today – in the process of each login, each bank transfer, each secure message. Its existence is unknown to the majority of people. And the ones that know are in a great hurry to put it back on before it gets late.
This article dissects the reasons as to why both RSA and ECC, which are the most widely used encryption systems globally, are on borrowed time, what they are being replaced by, and why for organizations that fail to adhere to the clock, already have a real cause to worry. Camp is the kind of background information every developer, every security professional, every business owner or even that bored individual who cares about how their data remains confidential should have.
Table of Contents
What RSA and ECC Actually Do
It is worth having a clue as to what these systems are guarding before proceeding to why they are vulnerable.
Both RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography) are cryptographic systems, which are a form of cryptography, and in particular public-key cryptography. They support HTTPS, VPNs, secure emails, digital signatures and majority of the authentication systems used in the internet world. In case your browser displays a padlock the likelihood that RSA or ECC is working behind the scenes is very high indeed.
Both systems utilize math problems that are incredibly difficult to solve using the classical computers at any sensible time.
The security of RSA lies in integer factorization: It is simple to multiply two large primes, and extremely hard to undo the process – to multiply them and compute the two original primes. An RSA key of 2048 bits in size implies that the semiprime underlying it is so large that a classical computer can take millions of years to factor it in brute force.
ECC follows a different path and it is based on elliptic curves discrete logarithm problem. The mathematics are different, though the principle is the same: computationally asymmetric. Simple to calculate upwards whereas almost impossible without the secret key.
This assumption of hard math has been true over decades. The thing is that it only holds in case of classical computers.
How Quantum Computing Breaks the Assumption
Shor’s Algorithm: The Core Threat
Everything comes into zero in 1994 when mathematician Peter Shor published an algorithm that makes everything different. The algorithm developed by Shor that can run on a quantum computer has the capacity to obtain the factors of large integers, as well as resolve the problems of discrete logarithms within the time of polynomials, rather than determining them exponentially.
That difference is a big difference. Attempts to use classical computers to solve RSA-2048 require exponential time – the problem becomes so exponentially difficult as to become virtually impossible in practice. Shor’s algorithm flips that. With sufficiently large quantum computer, it becomes feasible to factor the RSA semiprime or get the discrete log problem of ECC solvable.
What that would mean in practice: it might have a powerful enough quantum machine that it can generate a private key using a public key. It may mascard as servers, break signatures, decrypt communicates overheard. Any supposition on which the security of RSA and ECC is based falls.
I have read a few of the technical explainers of the post-quantum documentation and security research papers of NIST in preparing this. It should be a regular pattern erased by a patch that there is no patch to the algorithm of Shor. The only way to make RSA or ECC quantum-resistant is to increase the size of the keys, at least to a degree useful. The algorithm breaks the math structure.
What About Symmetric Encryption?
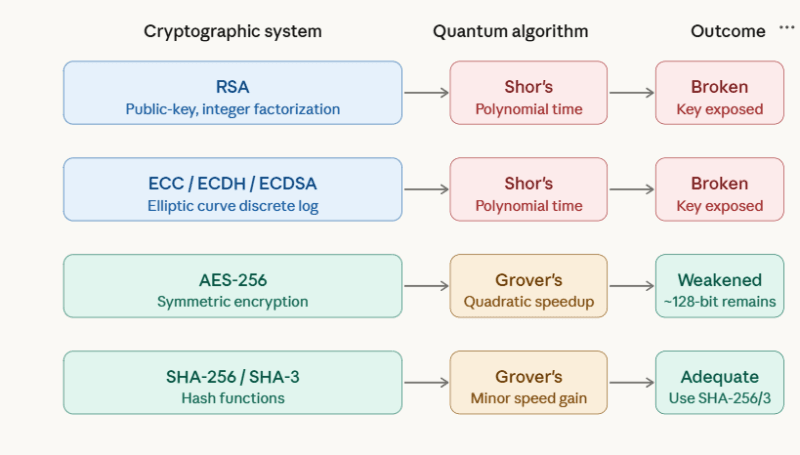
Nothing breaks under equal measure. Symmetric keys such as AES and hash cryptography functions such as SHA-256 are a little more threatened by quantum computing: Grovers algorithm.
Grovers offer quadratic increment in the search of unsorted data. This is applied to brute-forcing a symmetric key, and as a consequence, effectively reducing AES-128 to around 64-bit protection against a quantum attacker – weak. But AES-256? That becomes about 128-bit quantum security, which is still thought to be sufficient in the predictable future.
This leads to the consequence that the quantum threat 101 story is more precisely concerned with public-key cryptography RSA, ECC, Diffie-Hellman, ECDH, ECDSA, Ed25519 and its derivatives. Symmetric encryption and hashing are not disposed but get a size increase.
The following graph illustrates how the algorithm by Shor achieves the goal of satisfying public-key systems but the algorithm by Grover only weakens symmetric ones:
The Harvest Now, Decrypt Later Problem
Why the Threat Is Already Active
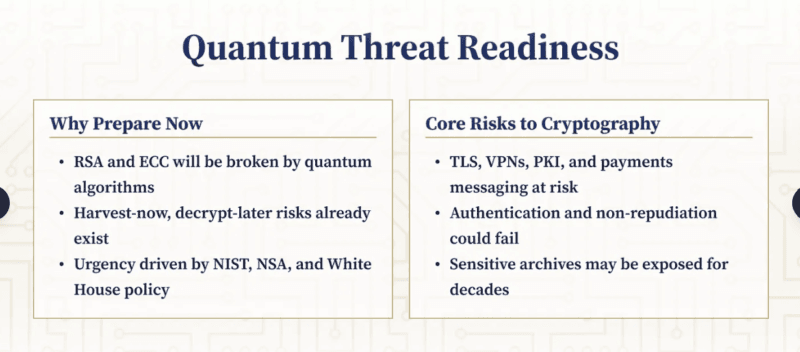
This is where it stings, in that organizations need not wait till they are at the point of losing a working quantum computer to jeopardy. It is another type of attack that is already in process.
This technique is referred to as a harvest now, decrypt later (HNDL). Encrypted network traffic capture and storage and manipulation by nation-state actors and advanced adversaries is already a reality today -SSL/TLS sessions, VPN tunnels, encrypted file e-mails.
They can’t read it now. The presumption though is that once a cryptographically relevant quantum computer (CRQC) is built, they will have an opportunity to reverse all that they have stored.
The review of the experience with enterprise security assessments indicates that this threat is usually evaded as hypothetical. It isn’t. Storage cost storage of bulk traffic has been reduced into almost zero. The motivation of collect now is high among nation states. Government
market records, medical records, legal agreements, proprietary studies, intelligence records – any data of sensitivity that has long survival is within the scope.
The vital variable is the data lifetime. Suppose that nowadays the information that you are protecting has to stay within the wall of the secret but only two years, it is not that HNDL is your biggest thorn. However, when it must remain confidential, at least ten years and longer, as the vast majority of sensitive enterprise and government information, the clock has already begun to run on harvesting now.
What Data Is Actually at Risk
Encrypted data is not equally risky. The most exposed categories of HNDL:
- The greatest motivators in the collection of information are the government and military communications- the foreign intelligence services are the most motivated.
- Personal identifiers (permanent) and healthcare historical records (long retention) It is in permanent form and has long retention periods.
- Intellectual property and trade secrets – competitive advantage is decades old.
- Contracts, compliance documentation, and audit trails Long-term financial and legal duty agreements.
- PKI infrastructure and root certificates – failure in this case is contagious throughout down the chain. The exposure of the HNDL is low in the case of most consumer data – a login session, a short-lived API call. However, organizations dealing with any of the above categories are well advised to consider this as a risk in the present day and not in future.
Timelines and the Road to Q-Day
Where Quantum Hardware Actually Stands
Among the transparent disadvantages in this area is that no one knows when a cryptographically significant quantum computer (CRQC) will be implemented, that is, one that is capable of successfully executing Shor’s algorithm against practical sized RSA-2048 or ECC-256 keys.
What the studies have shown is that the trend has increased. Recent generalization lowered the simulation cost among qubits and gates to break RSA making previous overall margins of comfort smaller.
Current estimates indicate that RSA-1024 may be compromised as early as the 2028-2030 period with RSA-2048 and other possible future standards challenged as early as the early-to-middle 2030s, under realistic research- lab conditions.
The utility-scale quantum computing program of DARPA, (and similar government-evenly funded programs of other nations) are an indication of a planned effort towards useful quantum machines in (approximately) the same international timeline of either the early- or mid-2030s.
Why Migration Timelines Start Now
The fact that even in 2033 when “Q-day” occurs, organizations may still have time to prepare does not imply that organizations will have until 2032 before they begin preparing.
The upgrading of the cryptographic infrastructure is traditionally slow. The cryptography in a large enterprise or government agency – among PKI, TLS settings, VPN stacks, firmware, IoT agents, code-signing systems, and other protocols of their own – can usually require five to ten years or more to update.
The regulatory calculus is simple: when full migration to post-quantum cryptography must take place by 2030-2035 then it must begin to be planned now. Bodies that deal in standards are already making this an urgent need and not an option in future.
Three post-quantum crypto statements have been completed in the NIST: FIPS 203 (ML-KEM, which uses CRYSTALS-Kyber), FIPS 204 (ML-DSA which uses CRYSTALS-Dilithium), and FIPS 205 (SLH-DSA which uses SPHINCS+).
The NSA has introduced the CNSA 2.0 model that requires the adoption of PQC within the national security systems by approximately 2030. The depression of RSA-2048 and ECC-256 has an estimated date of 2030-2035.
Post-Quantum Cryptography: What’s Replacing RSA and ECC
The New Math Behind PQC
Post-quantum cryptography does not make use of quantum computers, but is classical cryptography that is resistant to quantum attacks. The most important change is to move out of the problems that can be solved by the algorithm that Shor proposes (factoring, discrete logs) and to math problems where the quantum machines are thought to remain hard.
The final standards that are adopted in NIST are based on:
- Here is lattice-based cryptography Lattice-based cryptography ML-KEM (Kyber): ML-DSA (Dilithium). Security basis is based on the hardness of such problems as Learning With Errors (LWE) in high-dimensional mathematical lattices. These have no known quantum algorithm that gets a useful speedup exploited by any known quantum algorithm.
- Hash-based signatures SLH-DSA (SPHINCS+) relies only on the security of cryptographic hash functions, which are only weakened by the Grover algorithm.
- Code-based schemes and multivariate schemes – another family under study to reduce redundancy, as no one individual PQC family has so far had decades of cryptanalytic pressure cash in on it.
The Trade-offs Worth Knowing
PQC isn’t a straight swap. Security architects and developers should be familiar with real practical costs.
The lattice based schemes have much larger public keys and ciphertext than their RSA or ECT counterparts. The size of ML-KEM keys has been specified in kilobytes instead of hundreds of bytes. PQC-enabled TLS pilot programs report observations of about 20-35% overhead in the handshake to what current ECDH-based systems are observing.
That impacts bandwidth, storage, and latency – especially in limited resource systems, such as the IoT devices, embedded hardware, and high throughput financial infrastructure. It is not impossible without planning.
It is one of the focal challenges the person undertaking Post-Quantum Cryptography Migration will hit within no time it is not a simple configuration change. It may commonly imply the revision of libraries, protocols, hardware security modules (HSMs), and the machinery supporting the key generation, distribution, and warehousing.
What’s Already Deployed and What’s Just Starting
What Exists in 2026
The migration process is taking place in the locations that are well situated to relocate swiftly.
Major browsers and hyperscalers have been testing or implementing hybrid key exchange in TLS – executing ML-KEM and classical ECDH simultaneously, preventing connection security even in case one of the two algorithms is subsequently broken.
Prior to the final assignment of the NIST standards, Google, Cloudflare, and others started experimenting with hybrid PQC-TLS designs in production.
The three standards in the end (FIPS 203, 204, 205) of NIST are published and stable. VPN heavyweight vendors, certificate vendors and enterprise security vendors have started releasing products or previewing PQC-enabled products.
Profiles, hybrid patterns, and transport-layer guidelines have been published in the IETF, ETSI and ENISA to guide the architects in actually implementing these changes.
Open-source tooling exists. PQC algorithms have their reference implementations in the liboqs project. SDKs by vendors are starting to have support of ML-KEM and ML-DSA.
What’s Just Beginning
The more difficult and slow is the organizational side. Top-down inventory Most of the enterprises have not yet done their crypto inventory, which is an organized audit of the location of RSA and ECC throughout their infrastructure. Migration planning is in the dark without such an inventory.
The idea that is gaining more and more following is cargo-agility: building systems in such a way that cryptographic code undergoes modular and swappable implementation in cryptographic algorithms. The RSA-2048 + SHA-256 based application developed today will need code modification to port.
The algorithms in a crypto-agile system can be updated by means of configuration. The agile design of today significantly lowers the cost of the transition in the end.
Even the regulatory pressure is formalizing. The US national security systems deadlines are hard on CNSA 2.0. National cybersecurity agencies such as those in Europe like ENISA, and various countries are releasing statements on mobile and network migration with specific deadlines. Government contracts and regulated industries are starting to publish PQC readiness in the form of procurement and compliance requirements although in enterprises.
The Road Ahead and How to Start
A Practical Starting Point
Migration to a post-quantum cryptography should be a project of significant magnitude, and it will take years before a large organization is fully migrated. But these are the definite first steps that will be really noticed:
1. cryptographic exposure: inventory. Determine the location of RSA and ECC – TLS certificate, VPN setups, S/MIME, code-signing pipelines, IoT, HSM, a firm-firm connectivity. You have no thing to migrate before you can find it.
2. Determine your lifetime risk of data. What information in your organization should be confidential within ten or more years? That’s your HNDL exposure. Protection of those data flows should come initially.
3. Follow the NIST standards. The final baselines are stable and FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA). Solutions to the vendor which are not suiting should be taken with caution.
4. Test hybrid deployments. The suggested intermediate solution is to run ML-KEM and ECDH in TLS set-ups and VPN set-ups. It offers quantum resistance to classical crypto without forsaking the classical standards to the years of real world experience.
5. Plan for crypto-agility. Where new systems are being constructed or old ones great refactored, alcohol construct layers of abstraction. It is less expensive to construct this today as opposed to retrofitting later.
To further support the technical background, my experience led me towards two specific more useful external materials: the ENISA Post-Quantum Cryptography Migration report to get the migration strategy and organizational advice, and the ETSI Quantum Safe Cryptography white paper to give a clear technical explanation of why at the time the existing cryptography is vulnerable and how quantum-safe alternatives compare.
Trust Booster External links: Anchor text:
- along with the titles: – https://csrc.nist.gov/projects/post-quantum-cryptography
- Directional or anarchic implementation: ENISA PQC Migration Guidance, this article specifies steps intended for achieving a marginal benefit realization process. https://www.enisa.europa.eu/publications/post-quantum-cryptography-current-state-and-quantum-mitigation
Wrapping Up
RSA and ECC won’t last is not the main point of Quantum Threat 101: Why RSA and ECC Won’t Last. The relevant quantum computers that have cryptographically significant capability of implementing the algorithm given by Shor at scale are not available yet.
But the direction is evident, harvest-now-decrypt-later is already operational in the case of long-lived sensitive data, and it will take years to move about, not months.
As are RSA and ECC, they are not retiring by the flip of a coin. However, those organizations beginning their Post-Quantum Cryptography Migration planning today will create inventory, risk assessment, hybrid deployments, crypto-agility options which will exist in 2030. The ones that wait won’t.
The mathematical problem which is the basis of your present security is not faulty. It is simply weak in a very particular manner, and its weakness is a timeline that is coming to be known upon. That’s enough to act on.
I’m a technology writer with a passion for AI and digital marketing. I create engaging and useful content that bridges the gap between complex technology concepts and digital technologies. My writing makes the process easy and curious. and encourage participation I continue to research innovation and technology. Let’s connect and talk technology!