Open-source software, silently rules the world. It is in banking applications, in hospital systems, cloud-based infrastructure and in the tools developers are dealing with day-to-day. However, the greater the dependence we have on it, the more vulnerable we are likely to be- and OSS governance is still lagging behind.
This paper identifies the current state of the security of OSS: the policies already underway, the tools that are currently being actively used, and the gaps left there. Whether you are a developer who has to maintain dependencies, compliance officer who has to work with license reviews, or security engineer who has to develop incident response plans – there is something worth knowing.
Table of Contents
Why OSS Governance Finally Has Everyone’s Attention
The open-source security has been considered as a peripheral activity over time. They freely used projects, which were hardly audited and never formally tracked. Then came SolarWinds. Then Log4Shell. Then XZ Utils in 2024 – a near-disaster deepwater to supply chain that made it into one of the most popular compression libraries used by Linux operating systems.
All of those incidents reflected the same underlying issue: organisations in their consumption of open-source code did not actually know what they were getting in it and where it originated and was being maintained.
I have applied open-source components in the production setting where the latest commit was three years ago. Nobody flagged it. Nobody checked. It is that gap in governance in the practice of things and it is what regulators and security institutions are now attempting to seal.
What’s Already Here: The Regulatory and Tooling Landscape
The U.S. Securing Open Source Software Act
The Securing Open Source Software Act that passed through the Senate Homeland Security and Governmental Affairs Committee established the atmosphere of accountability of Open Source at the federal level. It instructed CISA to examine the use of open-source software by the critical infrastructure and create a risk framework of federal agencies.
The legislation does not govern the open-source community per se – it takes care of the consumption of OSS by the government. Nevertheless, the implication on the practice of adoption of enterprises has been immense. The new procurement teams are asking questions that they never asked earlier.
CISA’s OSS Security Roadmap
CISA published an open-source security roadmap specifically which outlined four general objectives: enhancing awareness about the use of OSS in critical infrastructure, minimizing risk to it, making the ecosystem as a whole a safer security environment, and ensuring better response to it in the community.
My experience showed that in the vast majority of organisations, goal one, which is simple visibility of what OSS they run, is still not achieved. That is what CISA roadmap is basing on and it is the correct decision.
The EU Cyber Resilience Act (CRA)
The largest regulatory change to the open-source in Europe is the Cyber Resilience Act by the EU. It implements obligatory security standards on products containing digital components – and although it makes exemptions of non-commercial OSS projects, commercial products incorporating an open-source component are plainly in its range.
Every compliance team in the EU is already thinking about the September of 2026 deadline of reporting. According to the analysis of CRA, the software producers cannot continue to think of their open-source dependencies as someone else’s security problem.
Open-Source License Compliance and Security Reviews
Two disciplines that most teams continue to regard as dissimilar, despite having a direct connection are license compliance and security. They’re not.
Proprietary codebase dependency with GPL license is more than a mere legal risk: It tends to indicate that not more than merely a cursory review of the components was conducted during the intake process. And when intake reviews are bypassed during the licensing, they tend to be avoided on the security.
What a Proper OSS Review Looks Like
An excellent OSS governance begins at the adoption stage. The following are teams that should be running before a library enters into codebase:
- Classification of the license: Would it be MIT, Apache 2.0, GPL, or LGPL? What are the redistribution requirements?
- vulnerability scanning: Does this package contain known CVEs? Is it actively patched?
- Scorecard evaluation: OpenSSF Scorecard assigns a score to every project on the basis of security hygiene: the security of the branches, signed releases, dependency updates, CI/CD practices.
- Maintainer activity check – It shall be a liability rather than an asset to a project having a maintainer that has not been active in the recent past.
I have observed during security inspections that the smaller risk is types of licensing problem which are frequently reported to the teams but rather maintenance abandonment which is bigger in risk. A ticking clock is a library which has a clean license but no active maintainer.
There are common tools such as FOSSA, TLDR Legal and the OWASP Free for Open Source Application Security Tools list which are commonly used to do this. They do not interpret as it is done by human judgment, but they identify what automated CI cannot.
Forking, Maintaining, and Updating Dependencies
When Forking Makes Sense – and When It Doesn’t
It is easy to forking to an open-source project. In reality, it entails taking up long term maintenance liability. All the upstream security patches that are released now require to be reviewed and merged manually. All the dependencies that the forked project has had is your dependency.
Forking is done to prevent a change in licensing or customise behaviour in organisations. That’s legitimate. But I have internally forked libraries which were 2 releases behind upstream, and which contained unfixed CVEs that the upstream project had addressed several months ago.
The guideline: engage only in fork-ups at which you possess the internal engineering capability to service it. Elsewhere, submit patches to develop instead.
Keeping Dependencies Updated at Scale
Dependency drift is a typical type of OSS security failure and the one that can be most effectively avoided. Dependency-checks are automated (such as Dependabot, Renovate, and OWASP Dependency-Check) and identify the known vulnerabilities in a lock file.
The challenge isn’t tooling. It’s process. PRs accumulate like automobiles, and unless triaged in the workflow, they are either combined unintentionally or left unattended at all. Neither is good.
The more proper solution: any dependency update should be treated just like any other patch, and each has to be triaged on its merit, staged and released with a rationale in the documentation. It’s slower, but it’s auditable.
Community vs. Commercial Support Trade-offs
The Reality of Community-Supported OSS
Majority of these open-source projects are being supported by few people who may either be unpaid or employed part-time. The Linux Foundation 2025 State of Open Source report established that a substantial size of important OSS infrastructure was maintained by less than ten individuals across the world.
It is not a critique of the open-source model, but a structural fact, which ought to be taken into consideration by organisations in their risk assessment. Community support entails: it is likely to be made fixed, however timelines become unpredictable and there is no SLA.
When Commercial Support Is Worth It
Distributions of open-source software like Red Hat Enterprise Linux, Elastic offerings operated under management, or Confluent to run Kafka, do provide something that the community projects are not capable of providing: response times on a contract basis, fixed patch update schedules, and full-time support engineers.
In infrastructure which interacts with production systems or controlled information, commercial support cost is frequently compensated by the reduction of risk itself. The trade-off is cost of vendor lock in and license cost, which increases with usage.
My practice revealed that the correct answer is almost always to come up with a hybrid one: community packaging of internal tooling, commercial support of everything in contact with MBA or a compliance sensitivity.
Software Supply Chain Security and the SBOM Requirement
Software Supply Chain Security has ceased to be a niche issue to a boardroom one. SBOMs (Software Bills of Materials) became the main instrument towards the goal of the White House OS3I initiative.
The key differentiator is that an SBOM just happens to be a list of ingredients of software: each component, each library, each dependency, and its version version and license details. SBOM production of the software sold to the federal government was required by the Executive Order on Cybersecurity (EO 14028). CRA is imposing the same demands in the EU market.
SLSA, Scorecard, and Sigstore – The Tooling Trifecta
The OpenSSF ecosystem has three tools that are becoming common procedures:
- SLSA ( Supply Chain Levels for Software Artifacts) A system used to counter the integrity of software build processes. It outlines four degrees of supply chain security ranging between basic and the hermetically sealed constructions.
- OpenSSF Scorecard – The scorecard is an automated scoring mechanism of security practices of a project. It is especially handy when being used to curtail high-risk packages, particularly during the process of evaluating the procurement process.
- Sigstore The Cryptographic signing of software artifacts. It allows one to confirm that a package was not always modified since the time it was shipped by a developer on their machine and yours.
These tools do not act independently. The actual payoff follows the incorporation of them into CI/CD pipelines to the effect that each of the builds is automatically tested, signed and testable.
Incident Response: Coordinating With OSS Projects
The Governance Gap in OSS Incident Response
When a weak spot has been identified in a commercial product, there is a vendor to contact. Under open-source, this is not as clear-cut a procedure – and that vague place will cost time in the incidents.
Coordinated disclosure is the usual procedure: the discoverer informs the security contact to the project (where such exists), settles on a process of disclosure, and does not make public any information which is fixable until a fix. The issue lies in the fact that not all OSS projects have an official security point of contact or disclosure procedure.
This is specifically the focus of CISA roadmap which drives OSS projects to use security policies – a SECURITY.md file in the repository, a CVE Numbering Authority (CNA) relationship, and a response timeline.
What Organisations Should Do Before an Incident Happens
It is too late to wait until a vulnerability occurs to develop a response strategy. The operational processes which are important:
- Mapped your OSS exposure Know which packages are under production, what are their maintainers and how do they rollback.
- Follow alerts and reports Subscribe to GitHub Security Advisories, OSV.dev, and the NVD feed are free. Use them.
- Establish an internal escalation route – When a critical CVE is dropped at 2 am who takes the call on emergency patching or emergency mitigation controls?
- Participate upstream- When your organisation utilises a project on a regular basis, add value to it. Known teams receive prior warnings of any security problems.
In 2024, developer of XZ Utils incident discovered the anomalous CPU usage, which was discovered. That is not a process that is luck. Luck doesn’t scale.
What’s Just Beginning: OSS Governance in 2026 and Beyond
OpenSSF’s 2026 Roadmap
The OpenSSF released its 2026 community roadmap in three headline themes of AI/ML security in OSS, CRA alignment, and wider adoption of the OpenSSF Baseline, a minimum security standard of open-source projects.
Of great importance is the AI angle. The conventional review that follows the entry of AI-generated code to open-source repositories falters as it enters in large numbers. For more intuitive error code can be syntactically correct code that has implications of logic errors or deliberate backdoors, such that they are not detected by human stylistic analysis at speed.
Memory-Safe Languages and Package Repository Security
Instructional support of the movement of memory-safe languages Rust, Go, and others into institutional support is building up. The ONCD report in the white house was specifically clear in advocating the move towards abandoning C and C++ in favour of new system development where feasible.
The other frontier is the security of package repository. There have been malicious package incidents in PyPI, npm and RubyGems. Repository-level security frameworks, such as ensuring that publishers are verified, are being standardised, malware scanning is automated, and that maintainers use a mandatory 2FA.
OSPOs as Governance Infrastructure
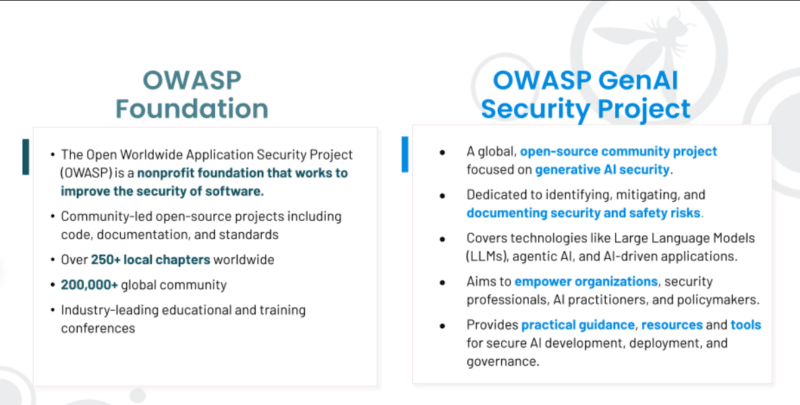
OSPOs are becoming common in large organisations. The handbook Good Governance Initiative by the OSPO Alliance provides instructions on organizing an OSPO: policy structures, how to contribute, license review procedures, and security audit procedures.
Possessions of organisations with OSPOs provide improved OSS security posture, not necessarily because OSPOs are magic, but because somebody is now held accountable. Such accountability is all that transformation of behaviour.
Free Resources Worth Bookmarking
To any person developing OSS governance skills, funds free:
- OpenSSF Training: OpenSSA.org/training also provides 10+ digital badge free courses, such as Developing Secure Software, and SLSA: An Introduction.
- OWASP Top 10 OSS Risks: This is a free taxonomy of the top ten most significant risks of open-source consumption – owasp.org.
- Roybyro Volume: Guide to Open Source Security Brucenaire, Startup board, and Comment cards by Mike Royal on the GitHub repository Open Source Security Guide.
The Bottom Line
OSS governance is not a box. It is a continuous operation field that involves law, engineering, security, and procurement working together in one field.
The regulatory landscape is becoming increasingly strict – the CRA 2026 deadline is not mythical, federal SBOM is growing, and the OWASP risk taxonomy is already another one that must be met in the provision of security audits. Companies who perceive open-source as an infrastructure that is not charged, but requires no maintenance are the government overheads are going to find that defence an inexpensive service.
The tools exist. The frameworks exist. The missing element in most organisations is the internal accountability framework – an OSPO, a written policy, an individual whose role involves understanding what open-source software the organisation operates and whether it is safe.
That’s where the work is.
I’m a technology writer with a passion for AI and digital marketing. I create engaging and useful content that bridges the gap between complex technology concepts and digital technologies. My writing makes the process easy and curious. and encourage participation I continue to research innovation and technology. Let’s connect and talk technology!