Look, the vast majority of people do not think about the security of their webpage until something has gone awry: their home page is defaced, they get a Google warning or even worse, they lose customers walking out of the door with their data under their arm. I have tested a number of tools on the live and staging environments and I was not surprised that the process can be complex. It was the number of holes that can be missed by the mere virtue of no one having bothered to look at it.
This guide disaggregates vulnerability testing of the site security in 2026 – what it is, why it remains relevant (more than ever), what tools are available, and how to construct a process that not fall-apart after a single sprint.
Table of Contents
What Is Website Security Vulnerability Testing?
Simply put, testing of the vulnerability of websites is the action of identifying and verifying the vulnerabilities of web applications, APIs, and host infrastructure in a safe and secure manner before attackers can do it.
An adequate test normally incorporates a number of stages:
- Recon and information gathering Tracing the tech stack, services that are exposed, and entry points.
- Configuration verification HTTPS, security headers, hardening of the server
- Authentication and access control testing – authentication, role-based access, privilege escalation
- Input validation testing Validation of XSS, SQL, IDOR, and broken business logic.
- Exploitation and proof-of-concept- safely test and validate actual impact, and report.
The most comprehensive publicly available reference to operating this end-to-end is the OWASP Web Security Testing Guide (WSTG). It’s where most professional checklists start.
Why It Still Matters in 2026 And Why the Stakes Are Higher
The OWASP Top Ten Shifted Again
There was a significant change in the OWASP Top Ten 2025: Broken Access Control remains on the first place, Security Misconfiguration crossed to the second one, and the new category Software Supply Chain Failures was introduced. The latter one is worth listening to.
These are not theoretical issues when it comes to WordPress-type websites or small business platforms. Wrongly configured servers, default passwords of administrators, out-of-date plugs, these are the real entry points of attackers. The outcome: account takeovers, SEO spam on your site, data breach, or ransomware via hacked hosting consoles.
AI Changed Both Sides of the Table
It is at this point that 2026 becomes truly different. AI has now entered the sphere of the occurrence of attacks and the construction of defenses.
AI-enhanced dynamic testing tools are now able to identify both traditional web vulnerabilities and AI-based ones such as prompt injection or AI-mediated command injection. In the meantime, the 2026 LLM security environment demonstrates language models taking on new functions as orchestration layers – invoking APIs, decoding sensitive inputs, invoking actions on the back-end – with completely new failure modes introduced.
In case a site deploys an AI chatbot or any other feature powered with LLM, such a surface should be counted as a part of testable scope. Here is where LLM Supply Chain Security is actually taken into account; not merely a scholarly study. It was my experience that most teams that add AI features do not update their threat models to understand these new entry points that causes a silent gap.
Core Testing Approaches: Manual vs. Automated
Manual Testing Still Has a Place
Manual testing includes creating ad hoc payloads, testing through authentication tests by hand, and exploring business logic that auto tools cannot reason about. Burp Suite, OWASP ZAP, and Postman are some of the tools that can be effective here- particularly with APIs.
A 2025 manual testing guide suggests using a step by step process:
- Enumerate tech stack, frameworks, endpoints
- Craft targeted auth, access control and input validation payloads.
- Safely exploit findings and document proof-of-concept with screenshots I have found that teams that omit manual testing virtually never detect logic bugs; the ones in which the tool reports pass, but a real attacker discovers a bypass.
The Automated Tool Stack
Automated testing encompasses more at a higher speed. The stack today divides into:
- SAST – scanned at build time scans source or bytecode to insecure patterns.
- DAAST – live game scanning of running applications (OWASP ZAP, Burp scanner)
- IAST -instrumented runtime analysis active testing.
- SCA dependency and supply-chain scanning of known CVEs in libraries and plugins.
- RASP – runtime defense that is integrated into the application.
These have become no longer optional in integrating into a CI/CD pipeline by teams that ship frequently. Quick wins include automated dependency checks and implementing security headers that can be quickly recovered before it gets to production.
My Tested Tool Recommendations for 2026
PortSwigger Web Security Academy
Free, continuously updated and based on lifelike labs. The platform includes SQL injection, XSS, CSRF, broken authentication, SSRF, and JWT against attacks and Web LLM against attacks. It’s where I would refer someone who would be beginning and only would like to be given the practical part without risking his or her life with the legal side.
Every subject covers theory, optional videos and live targets. The method -read, lab, translate to the real world -is an effective one.
OWASP ZAP
Being open-source and actively maintained, ZAP suits not only to a beginning user who does passive scans but also to an advanced user who can create his/her own attack scripts. It proved to be very useful as a pre-pass task that is automated and followed by further work.
TryHackMe and Hack The Box
The free courses on TryHackMe start with basics of web hacking in a orderly fashion, which would be helpful to develop muscle memory in regards to intercepting and manipulating requests. Hack The Box is more effective at that point, when the fundamentals are in place; it is rather a pressure-test than a formal training.
OWASP Juice Shop
A deliberately weak full-stack JavaScript application with all of the OWASP Top Ten. Install it on-premises with Docker, test Burp flows locally and find similar patterns in production or client sites. It can also be used to test WAF demos – when run together with an AWS WAF (in either a black box or white box way) it will become easy to see how WAF rules can block typical attack vectors and that deeper fixes will be designed.
Best Practices That Actually Hold Up in 2026
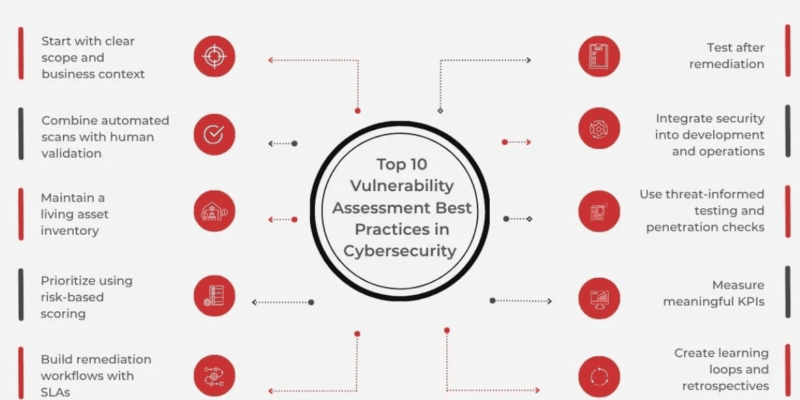
Technical Practices
Transport and Headers – Secure with TLS 1.3, allow HSTS, set Content Security Policy, X-Frame-Options, and X-Content-Type-Options. These are table stakes.
Authentication and access A powerful policy on passwords, multifactor authentication on all administrative interfaces, assignment of less privileged roles, and segregation of access with different accounts when performing administrative actions.
Patch management CMS core, themes, and plugins, server software, and databases need to be updated at regular intervals. Staging: Test first. On sites that are heavy in terms of the number of plugins, SCA scanning will find CVEs prior to them being turned into incidents.
WAF implementation-A web application firewall in front of the legacy or troublesome applications provides time to make appropriate correction.
Logging and monitoring: Monitoring anomalies in log traffic, configuring alerts, and responding to them. Logs that no one will read it are merely storage costs.
Process Habits
- Security testing embedded in the SDLC trounches annual audits invariably. Practical steps: Include SAST, dependency scans, and header checks to CI/CD.
- Run DAST also scans frequently, and then manual scans are done on critical workflows.
- Disregard findings as suggestions, instead of backlog items with due dates.
With a solo developer or a small software development team, a monthly security sprint and an automated CI hook can go a long way without the need to have a security engineer. Open- Source
GitHub and Open-Source Security: Worth Watching
Attack surface is also growing to include open-source ecosystems. The security features of GitHub such as the Dependabot alerts, secret scanning, and code scanning using CodeQL have now matured to an extent and are available free of charge to any public repositories.
These tools bring to the fore vulnerabilities before they are reported to the outside world in case teams use open-source dependencies or plug-ins. I have tried Dependabot on a few projects and I was pleasantly surprised with how it helps to identify outdated packages that are otherwise difficult to notice when analyzed manually.
Frequently Asked Questions
What’s the difference between vulnerability scanning and penetration testing?
Scanning is extremely automated and reveals possible problems on large scale – the problem of false positives is frequent. Testing of penetration includes both manual analysis and actual exploitation to demonstrate impact and chain weaknesses. Both are used in serious testing.
In what frequency are small business websites to be tested?
At present, it is recommended to perform continuous automated scans on a release basis, and vulnerability scans based on a schedule of not less than one a quarter and manual testing at least once a year. Additional testing upon significant changes – new features, CMS updates and updates to the plug-ins – is overhead justifiable.
What are the most vulnerable areas that should be prioritized?
OWASP Top Ten 2025 points to Broken Access Control, Security Misconfiguration, Software Supply Chain Failures, and Cryptographic Failures. To lock-down the administration in WordPress-style sites in particular: lock down administration, correct misconfigurations, clean up and refresh the plugins, and impose secure cookies and strong TLS.
Is it enough to operate scanners powered by AI?
No. AI-enhanced DAST detects additional -even some of the LLM-specific vulnerabilities-although such systems have their own emergent risks, which still require human rationality and business-logical insights. There is still a necessity to test manually, review the code and analyze the design.
TLight Does I have the legal right to exercise these skills?
Yes – PortSwigger Web Security Academy, TryHackMe, Hack The Box, and OWASP Juice Shop are all created with this in mind. Training on the systems that you have on or test on with certain written permission. All the rest are unlawful irrespective of the intent. Wrapping Up
In 2026, it doesn’t simply affect the developer of the site to test its integrity with security vulnerability, but also the business. The equipment is more authoritative, the area of assault is broadened (particularly with AI capabilities involved), and models, such as the WSTG framework created by OWASP, offer a concise course of action to be taken.
The difference between sites breached and those that are not typically is not the technical difficulty. The question is whether or not anyone ran tests and corrected what they discovered. Begin with the most basic examples, your headers, authorization, fixed dependencies, etc. and build upon it.
I’m a technology writer with a passion for AI and digital marketing. I create engaging and useful content that bridges the gap between complex technology concepts and digital technologies. My writing makes the process easy and curious. and encourage participation I continue to research innovation and technology. Let’s connect and talk technology!