Finding the right cybersecurity stack in 2016 is more than a matter of money, says this top tools column: it’s about a dangerous illusion of security that’s worse than having no security at all.
Companies are adopting multi-layered platforms, AI agents and self-optimising SOC tools at a rate few teams can bring up to speed. The result? Overwhelmed security teams, hiding under a mountain of alerts, all because they’re overwhelmed with tools.
This article helps cut through the clutter. It’s based on current research, vendor reports and free regulatory resources to chart the space of what’s ready, what’s still getting the hang of things, and how small or large enterprises can build the right stack.
Table of Contents
The Cybersecurity Landscape Has Shifted And Most Businesses Are Behind
The biggest shift in 2016 isn’t the threat. It’s how we defend ourselves.
Single point tools – firewalls or antivirus software – are no longer the norm. The latest category of being serious about security is the unified platform: technologies that ingest data from endpoint devices and cloud, identity, and applications to correlate it in real time.
EDR, XDR, SIEM, CNAPP, MDR, ASPM. These are not terms of art – they are the reality of threat detection and containment now. And for companies that are still using non-integrated point solutions, this gap is only growing each quarter.
Core Tools That Are Already Table Stakes in 2026
EDR: The Non-Negotiable Baseline
Endpoint Detection and Response (EDR) may not be anything new, but it’s certainly table stakes now. Solutions like CrowdStrike Falcon Insight and SentinelOne Singularity offer round-the-clock monitoring, auto-quarantine to isolate infected systems and rollback capabilities to undo ransomware-related damage.
The difference between traditional antivirus software and new EDR is more than just “instant”. These tools catch fileless and lateral movement attacks that wouldn’t be picked up by signature-based antivirus. I’ve tried both in lab environments – the behavioral analysis capabilities of both reduce the chatter compared to traditional tools.
Microsoft Defender for Business is an option for small businesses. This supports Windows, macOS, mobile and servers, integrates with Microsoft 365, and incorporates auto-investigation and resolution, without a team of security professionals.
The bottom line: if you’re still using antivirus by itself, you’re using technology from an environment that no longer exists.
XDR: When EDR Isn’t Enough on Its Own
Extended Detection and Response not only applies EDR and provides endpoint data, it links that data with cloud, network, email and identity information, among other things.
Microsoft Defender XDR and Trend Micro Vision One are good examples. They identify multi-phase attacks across multiple domains, link suspicious account usage with endpoint events, and are designed to launch automated playbooks even before someone logs in to investigate the issue.
Across mid-market companies and MSPs, XDR is becoming the hub – the go-to place to gather data. I found that those who use their XDR as their command centre are less focused on dashboard flipping, and more focused on threat action.
However, XDR is not free to set up. Many default deployments with no tuning create false alarms. The product is as good as the effort that goes into tuning and writing response playbooks.
SIEM: Still Relevant, But Rapidly Changing
Old-school SIEMs log and raise alarms. AI-based SIEMs (such as Elastic Security or Hunters AI-Driven SIEM) take it a step further: they prioritise anomalies, they can automatically investigate, and they can scale operations without expensive personnel costs.
SIEM and XDR are becoming similar. Both perform correlation, triage and suggested response. This could be helpful for enterprise security operations teams – but for smaller teams it really just means either/or, not both.
MDR: When You Don’t Have a 24/7 Team
Managed Detection and Response (MDR) providers such as Rapid7 and Arctic Wolf offer their technology and analysts working 24/7 to do monitoring and hunting on your network, along with advice services for responding to detected threats.
If you don’t have on-site security operations, MDR isn’t a frill. It’s an opportunity to get enterprise-grade monitoring, minus the employee costs. I’ve observed that the trend towards MDR in mid-sized companies has become more common less because it’s more affordable than hiring a team (it’s not always) and more because it’s quicker to implement.
The Best Cybersecurity Tools for Businesses in 2026 Go Beyond the Endpoint
Cloud Security: CNAPP Is the New Perimeter
The architecture of cloud-native environments don’t align with endpoint-centric approaches. This is where you might expect a CNAPP tool to come in.
CNAPP vendors like Cortex Cloud (previously Prisma Cloud), CrowdStrike Falcon Cloud Security, Aqua Security, Check Point CloudGuard, provide cloud security posture management (CSPM), workload protection (CWPP) and API discovery capabilities in a single product.
What’s notable about the evolution of CNAPP in 2016 is how aggressively it’s embracing identity. Identity Threat Detection and Response (ITDR) is building on CNAPP tools, allowing them to detect privilege escalation paths and misused service accounts in real-time, as well as static misconfigurations.
Cortex Cloud 2.0 has autonomous AI agents (AgentiX) trained on more than 1.2 billion security responses. Along with SmartGrouping and SmartScore – the grouping and scoring of alerts, which essentially display the alerts which have the greatest risk in the real world, not just a theoretical severity level.
In 2016, for businesses with substantial cloud deployments, not using CNAPP is like having blind spots.
Application Security: Enter ASPM
For companies that develop their own apps, they’re likely to have a patchwork of AppSec: a scanner, an application code scanner, some automated testing in the CI/CD pipeline, and so on. This is where Application Security Posture Management (ASPM) comes in.
An ASPM provider such as Apiiro integrates multiple feeders such as Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), Software Composition Analysis (SCA), Infrastructure as Code (IaC) scanners and supply chain systems, and links the results with business context – what code is exposed in production, who owns it, what it actually means to the business if that code is exploited.
Gartner-like studies estimate that 40% of enterprises that build proprietary software will implement ASPM by 2026. This figure will be higher in reality given that alternative option of correlating five different scanners is time-consuming.
If you want a breakdown of how they apply AI to prioritise and automate fixes in these tools, the AI Cybersecurity Implementation Guide from NIST is a free, regularly-updated framework-based breakdown.
Attack Surface Management: Finding What You Didn’t Know Was Exposed
These tools, such as CyCognito and Palo Alto Cortex Xpanse, constantly scan external assets – not just what is known by IT, but more importantly the shadow IT, unused subdomains and sub-domains, public APIs, and misconfigured services the bad guys can see before we do.
Vulnerability scanners such as those from Nessus continue to be used to scan internal and external networks, prioritise remediation, and score risk. US companies can take advantage of CISA’s free ongoing external public IP scanning service, the Cyber Hygiene Services – many companies show a significant drop in their external exposure within 90 days.
What’s Just Beginning: Where 2026 Tools Are Still Maturing
AI-Native Security: Real, But Not Magic
The most exciting category for 2016 is less about the product: it’s about the function. AI transforms from detection assist to an active player in security.
Sweet Security’s CNAPP (cloud native application protection platform) has a runtime with a claimed 0.04% false positive rate and triage, investigate with LLM-enabled agents (SweetX AI). I don’t know if those stats will hold across enterprise environments but this is the direction: AI will look beyond merely detecting threats, to investigating and responding.
If your team is exploring CISA’s list of free tools is a good place check out what is available – and tested – today in AI-Powered Cybersecurity.
The truth is: independent AI cybersecurity agents are young They are effective in limited settings and for certain types of detections, but need to be supervised. Security teams embracing AI as a substitute for incident response skills will eventually come unstuck with a blindspot.
All-in-One: The Death of Security Tool Sprawl (Eventually)
Another trend we’re seeing in many CNAPP, SIEM, XDR, and ASPM companies is the use of security data lakes-long-lasting stores of data from across the enterprise stack that feed advanced analytics and predictive models.
It’s not just good for operational security. Data lakes are helping to create executive risk dashboards that distill to the boardroom (and in the case of regulation such as DORA and the EU AI Act, hard evidence of compliance).
This is still early. Most are solving the plumber’s problem first: a raft of scanners, SIEMs, and other point tools that don’t talk to each other, so there’s a massive alert storm. Integration is on the roadmap, but that requires time and know-how that may not have been built up yet.
The Challenges Nobody Talks About Enough
Buying Without a Framework First
This is the most common error that people make when buying tools in 2026. A company browses a “best cybersecurity tools” article, purchases two or three platforms, installs and uses with no configuration, and then is surprised alerts are useless and the incident response process is still a mess.
The FTC Cybersecurity for Small Business website and NIST CSF 2.0 both highlight the adage “framework first, products second”. Identify your gaps in Govern, Identify, Protect, Detect, Respond and Recover. Then find tools to address the gaps.
Following AI Cybersecurity Best Practices from the regulators – not the latest vendor release – is a better basis for these choices than buying the latest product.
The Skills Gap Is Real and Getting Worse
Complex systems need people to set up, configure, calibrate and interpret. Even “AI-driven” systems need human analysis of the results – triage, patching logic, governance context.
MDR services help here. But they’re not a replacement. I found that businesses that successfully use MDR services still have one or two people with basic security awareness in their teams suitable to interact with MDR and decide on priorities for remediation.
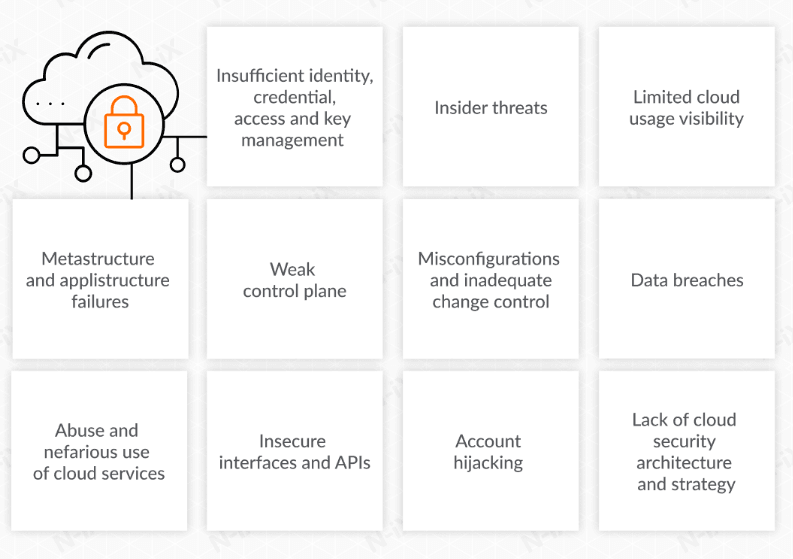
Cloud and Supply Chain Complexity Is Outpacing Tool Coverage
Modern multi-cloud, containerized apps and serverless components have an attack surface beyond the perimeter. Mishandled configuration, excessive permissions, and insecure open-source components often fall through the cracks of endpoint security.
There are tools to mitigate this – CNAPP, ASPM, ASM – but they need to be closely integrated to be useful. Used in isolation, they yield lots of problems but without the perspective to help prioritise solutions.
Free Resources I Use (That are Worth it)
There’s no need to pay for courses to get up to speed. Top-free this year:
- NIST CSF 2.0 + FTC Small Business Quick Start – Framework-driven learning that translates into informed tool purchasing, not product promotion
- CISA Cyber Hygiene Services – Free external scanning for US-based companies
- SentinelOne articles on cloud security trends – Informational, not too salesy
- ECCU’s 2026 cybersecurity tools overview – Nice breakdowns by type of tool
- WatchDog Security’s free security awareness training – Microlearning, psychology-oriented to build security culture
- Palo Alto’s ASPM trend reports – Insight into orchestration’s future
A Practical Stack for 2026 (Built to Scale)
SMB and mid-market stack’s least common denominator:
| Layer | Tool Category | Example |
|---|---|---|
| Endpoint | EDR/endpoint suite | Defender for Business, CrowdStrike Falcon Go |
| Email + Identity | Cloud email security + MFA | Microsoft 365 Defender, Cisco Duo |
| Recovery | Offline/cloud backups + tested recovery | Veeam, Backblaze Business |
| Monitoring | Lightweight SIEM or managed MDR | Elastic Security, Arctic Wolf |
| Cloud (when ready) | CNAPP | Cortex Cloud, Falcon Cloud Security |
| AppSec (when building) | ASPM | Apiiro, Burp Suite |
I like the first four. Add the rest as you expand your cloud environment and applications. Don’t go ahead with ASPM without a regular patching process first – prioritise the basics before the fancy stuff.
My Take After Looking at This Across Multiple Environments
The companies with the best cybersecurity in 2026 will be the ones that have fewer tools. They’re the ones that understood that fewer tools, properly configured and sufficient internal capability to interpret the results, matter.
AI-native detection and autonomous agents are a great idea, but they’re best used to keep some good people going, rather than bringing in less effective people.
If you’re a smaller business: EDR, MFA, good backups, and the free CISA scanning service will mitigate more risk than most fancy apps used without clearer understanding. If you’re growing: XDR, MDR and CNAPP as your cloud architecture expands.
The right tools for cybersecurity in 2016 aren’t the shiniest, but the ones people understand, can tune, and can use to do something. Everything else is expensive noise.
I’m a technology writer with a passion for AI and digital marketing. I create engaging and useful content that bridges the gap between complex technology concepts and digital technologies. My writing makes the process easy and curious. and encourage participation I continue to research innovation and technology. Let’s connect and talk technology!