Last updated on April 30th, 2026 at 03:01 pm
Security is usually something companies focus on if and when it fails. The email looks a little funny. An employee clicks the wrong link. One of your suppliers or manufacturers is compromised – and so are you.
That’s no longer worst-case. It’s Tuesday.
The good news? What sets apart the businesses that are woken from their dreams via cyber attack from those who recover quickly isn’t necessarily the size of the budget. It’s the planning they’ve put into their security. In this article, we’ll lay down the nuts and bolts of what’s working now, what’s on the horizon, and where most companies are going wrong.
Table of Contents
The Threat Landscape Has Shifted And Most Teams Haven’t Caught Up
This is the new reality: attacks are no longer “quick and dirty” They’re focused, programmatic and powered by AI.
Cyber criminals now know how to make machines search for weaknesses that people don’t know how to fix. They create scamming emails that don’t seem like scamming emails. They create viruses that change themselves to evade antivirus.
In fact, India is one of the top targets for phishing attacks – and those attacks have become more sophisticated. This is not insignificant. That your finance assistants get an email like that from the “CEO” happens all the time, from small businesses to multinational conglomerates.
The ransomware model has changed, too. Instead of just deleting data unless paid, they steal it and then threaten to release it. It’s about stealing the info, then demanding a ransom or we’ll release it. Cyber gangs are targeting the banking, manufacturing and healthcare industries.
Another arm is the attack on supply chains. If a vendor is compromised, it can be a back door into your network. What CISOs cite as their greatest challenge is getting third parties to comply – you can lock down your castle, but you can’t lock your neighbour’s.
What Zero Trust Actually Means in Practice
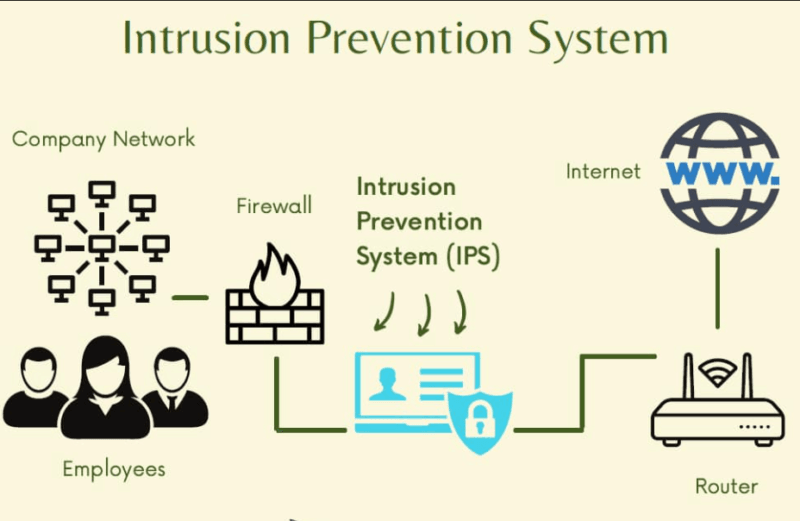
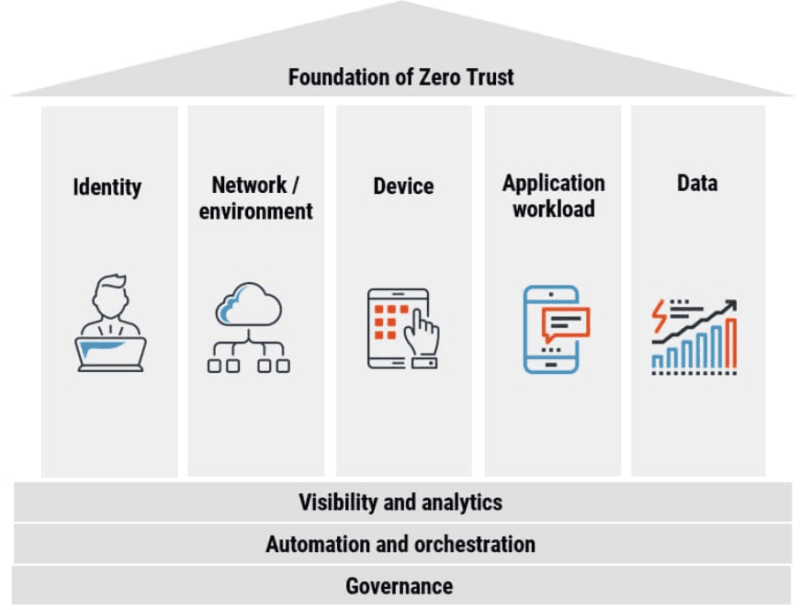
“Zero Trust” is a term that gets thrown around. It’s not a methodology, but an architecture choice, with discrete components.
Here’s the thinking: assume nothing within your network is secure. Multiple users, devices and requests are authenticated, even if they are physically in the office or not.
The Real Building Blocks of Zero Trust
The first is multi-factor authentication (MFA). But not multi-factor authentication (MFA) via text messages – those are currently being targeted by SIM swapping and MFA fatigue. App-based, hardware key-based or even biometric factors.
Micro-segmentation is dividing your network into smaller segments in a way that if an attacker seizes one, they will not be able to freely navigate and access other segments. I know of a company that didn’t do this and it was left wondering why all its systems went down when a single machine was compromised.
Least privilege means just that – users have minimum rights access to what they must do. Not everything. Not “just in case.” What they need.
Continuous monitoring completes the loop. Zero Trust is not a “set and forget” model. It’s a process that continues to verify identity, not only on initial login.
It’s better to do it in stages. Employees first, then the cloud workloads, then IoT/OT. Attention is typically short-lived and likely to result in push-back and compromise.
How AI Is Being Used on Both Sides of the Fight
Attackers have AI. It’s time for defenders to get some too – and it’s available now
AI-powered threat detection tools do what people simply can’t: evaluate huge amounts of data at once, detect behavioural anomalies in real time and cut down on false alarms that can chew up an analyst’s time. In my testing of a couple of these, there was a big improvement in the time it took to spot suspicious activity compared to a rule-based framework.
The advantages to a security operations center (SOC) include:
- Anomaly detection to spot things we would miss at 2am
- Cyber kill chain modeling that predicts attack vectors
- Quicker mean time to detect (MTTD) and mean time to respond (MTTR)
- Reduced alert fatigue as it weeds out the noise
Unfortunately, AI drives the attacks, too Malware with the ability to change its own code. Voice phishing attacks masquerading as CEOs to steal money. They’re no longer theoretical.
The solution is not to fear the use of artificial intelligence to guard against attacks, but to be proactive and use it.
What Most People Misunderstand About Cloud Security
Cloud is not secure. It means everyone has to think about security – and most teams don’t realise where the responsibility for security stops and the provider starts.
Mistakes in cloud configuration is an easily prevented cause of breaches. An unsecured Amazon S3 bucket, an API that isn’t authenticated, a cloud storage folder with incorrect permissions settings – it’s these sorts of things that make headlines.
This is where Cloud Access Security Brokers (CASBs) help. They help you discover the cloud applications being used by your company (even the unapproved ones), understand their risk, and automatically apply policies.
The process is find all, classify, take action. Discover all your resources, classify risks, then manage them.
For companies migrating to the cloud or hosting hybrid workloads, a good place to start is with the Cloud Security Best Practices Comprehensive guide that offers a bit more than “do whatever the cloud vendor tells you to do”.
The Quantum Threat Nobody Is Taking Seriously Enough
Why This Matters Even If Quantum Computers Don’t Exist Yet
In August 2024, the National Institute of Standards and Technology (NIST) finally released the first three adopted post-quantum cryptography (PQC) standards. These algorithms (ML-KEM, ML-DSA, and SLH-DSA) stand up to attacks by quantum computers.
Why now? Because of a “store now, decrypt later” attack. Hackers steal and store encrypted data now, and will read it later – once quantum computing becomes practical, in a decade or less according to experts.
Your valuable 2025 data, 2034 This is concerning for any long-lived data: IP, financial documents, medical records, government contracts.
Cryptographic auditing now – to determine which systems use flawed encryption – is a good place to start. The changeover won’t be instantaneous. These algorithms are not compatible with the old ones. They’re slower, they use differently-sized keys, and they introduce new complexities for exchanges.
Transitional hybrid approaches with both classical and post-quantum cryptography will be a stop-gap solution for most.
Where Cybersecurity Investments Actually Pay Off
Security investments are often seen as costs. This is misleading, and contributes to running security’s budget battles.
The cost of a data breach is more than $4.44 million, on average, globally. Danial time from a major incident is in the hundreds of thousands of dollars an hour. Ransomware recovery (even if you do not pay the ransom) includes forensic work, legal fees, customer and regulatory notification, fines and reputational damage.
When I break down the way companies measure return on investment (ROI) for the services they use, the best way I see to gauge it in four areas:
Avoiding breach costs – What does it cost to avoid an incident? If you’re managed detection and response prevents a ransomware attack, then that’s millions not lost.
Efficiency savings – Time efficiency with automation. It’s an hour that senior analysts focused on authentic threats.
Regulation adherence – Compliance with standards such as GDPR, HIPAA, or India’s DPDP Act, is not only about regulatory compliance. It means you can get clients in compliance-heavy sectors who practices won’t engage with non-compliant partners.
Customer trust – Security certifications, such as ISO 27001, demonstrate security competency. I’ve seen more enterprise purchasing processes involve a security questionnaire. Moving through that process is a real point of differentiation.
Picking the Right Tools Without Getting Overwhelmed
Security tools are a big, crowded market. All vendors claim to do it all.
For most small to medium sized firms, nothing needs to be complex. It needs to cover:
- Endpoint detection and response (EDR)
- Email security and anti-phishing
- Identity and access management (IAM) with MFA
- SIEM or log management
- Data backup and restore with restore procedures
For any teams trying to make decisions about options without having to reinvent the wheel, it’s helpful to look over a list of the Best Cybersecurity Tools for Businesses in 2026 to determine what is really needed, versus what is merely EBT.
The reality is that most security breaches happen because of a lack of basic security. They’re because your software wasn’t up-to-date, your passwords weren’t secure, or you had an employee who clicked on a phishing link.
Fix the basics first.
When You Need Outside Help And How to Find the Right Fit
It’s not always possible for every team to do this in-house. It’s not a flaw – it’s a reality.
This is where managed security service providers (MSSPs) and cybersecurity consulting companies come in. But not all MSSPs are created equal. Some are simply resellers with a computer screen. Others have the true expertise in threat intelligence, incident response and compliance management.
If your business is considering help from outside, what to look for in a cybersecurity consulting firm is as important as what products to purchase. Make sure you’re talking to firms who will thoroughly assess the situation and not just try to sell you a product.
Questions to ask a firm:
- How do you respond at 3am for an incident?
- Do you have any examples of how you’ve responded to a breach like the one we might get?
- What’s your approach to third-party and supply chain risk for our suppliers?
Building a Security Culture That Doesn’t Feel Like Compliance Training
What Actually Changes Employee Behavior
Yearly Slide Shows is Boring What I have noticed when examining how various organisations deal with security awareness is that those that do it well use “phishing” simulations, gamified challenges and role-specific security training programs, rather than just presentations.
The big change is tailoring training to work with a person’s role. Social engineering tricks might apply to your accounting department that don’t apply to your engineering department. Training should reflect that.
Publicly rewarding employees for handling suspicious emails, simulated attacks with (near) real-time feedback, and top-down support all play a role in making security an “everyone” issue and not a question of IT.
Free Resources Worth Actually Using
Don’t let limited resources stop you. Good free resources are available:
- Cybrary – learning paths from novice to expert, available anywhere
- LetsDefend – SOC skills using real scenarios
- SANS Cyber Aces – fundamentals: networking, operating system and system administration
- MIT OpenCourseWare – from real MIT teachers
- OWASP Foundation – vital information if you work with web app security
- EC-Council Free Courses – 24+ courses on cybersecurity, cloud computing and more
The Honest Bottom Line
To improve your business’s cybersecurity in 2016, it’s not about the biggest or most expensive. It’s about being deliberate.
Understand your true risk. Know what’s at stake, where it lies, and go outward. Adopt Zero Trust gradually. Don’t wait until an attack is imminent to deploy AI detection. Don’t wait to develop your quantum strategy.
It’s not the companies that responded to a breach. They’re the ones that considered security an operational reality – not a box to check.
I’m a technology writer with a passion for AI and digital marketing. I create engaging and useful content that bridges the gap between complex technology concepts and digital technologies. My writing makes the process easy and curious. and encourage participation I continue to research innovation and technology. Let’s connect and talk technology!



