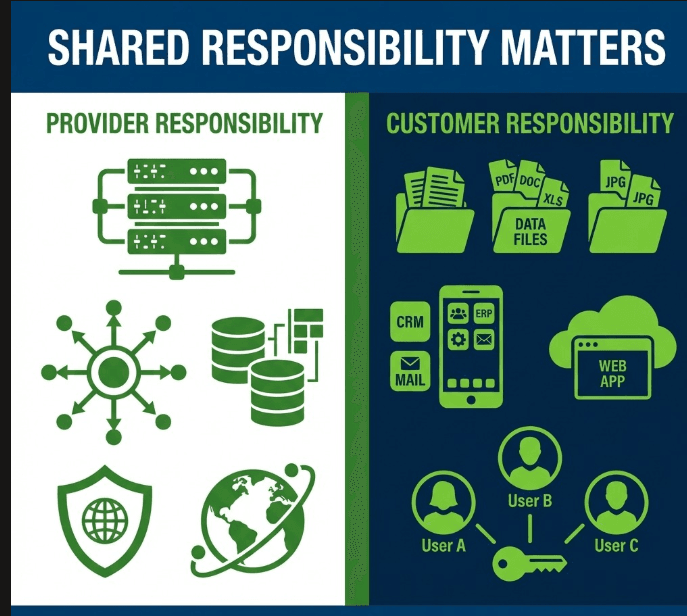
The general perception of most people is that the cloud is someone else’s problem to secure. It isn’t.
That is the difference that companies lose millions of dollars annually. The infrastructure is dealt with by the provider. You manage all of that in the upper layer – your identities, your settings, your data, your access policies. Lose either of that and what you still have is a gaping hole that will never be sealed up with enterprise level hardware.
There is no such thing as cloud security in 2026 with exotic threats. It has to be doing the fundamentals right and being able to stay abreast of a threat landscape that is evolving at a pace faster than most teams can keep pace. This article dissects what is already working, what is moving and what you actually need to be driven to, be it as a developer, a security engineer, or simply as someone who cares to know what is at stake.
Table of Contents
The Shared Responsibility Problem Nobody Talks About Honestly
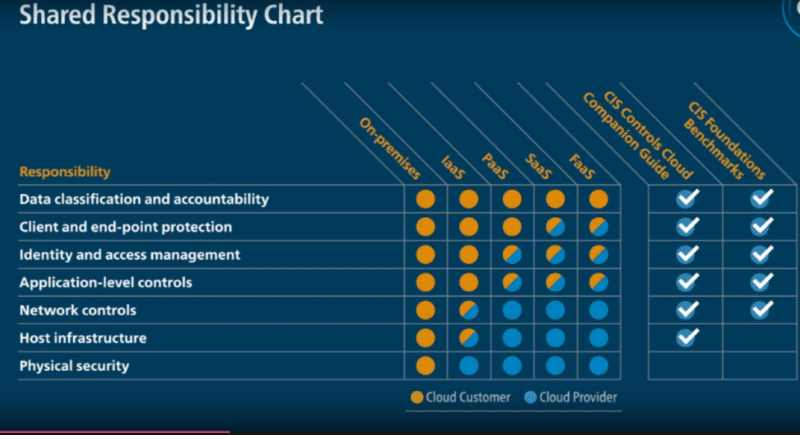
It is at this point that the majority of cloud security dialogues fail miserably because they perceive the shared responsibility concept as a given reality.
It isn’t.
Yes, AWS, Azure and GCP ensure physical infrastructure security. They fix hypervisor, administer hardware as well as network level redundancy. However, as soon as you deploy an incorrectly configured S3 bucket or grant an over generous IAM role, it is all your fault. This will be plainly indicated in the documentation of the provider. This is not the majority of breaches that are highly advanced cloud infrastructure attacks. They are wrong settings that are right before our eyes.
Scale is even a worse problem in 2026. Multi-cloud environments imply that now you are operating divergent control planes, with divergent IAM models or with divergent logging formats – all at once. The airtight policy on Azure might not be meaningful on GCP unless the logic enforcing it translates.
The workaround is not that complex. Begin with a good inside map of ownership. Then assert that the ownership of policy-as-code in such a way that it becomes automatic rather than annualized, assessed by hand.
What “Identity-First” Actually Means in Practice
Zero Trust is a term that is widely used to death, and it has lost its meaning. But the sense, the sense which stands behind all the buzzwords is really good, when you have shaken off the layer of buzzwords.
Identity-first security in practice implies that the perimeter of your network is no longer the main line of defence. Your identity layer is. That means:
- A single Identity Provider (IdP) that provides access by humans and machines.
- None of the mandatory MFA available, even to service accounts.
- Role-based and attribute-based access control are focused, controlled on the basis of what is really required.
- Mechanical verification of access to avoid access accumulating over time.
- Bots, pipelines and AI agents have short lived credentials not long living API keys stored in config files.
When I was testing in a simulated multiple cloud setting, the human accounts turned out to be the weakest in nearly every situation. They were service principals and had permission six months ago to do a one task, which had never been cleaned up. That is a trend that I have observed in case studies in the world as well.
In most cloud environments of mid-scale size, machine identities akin to service accounts, CI/CD pipelines, AI agents, have now surpassed human identities. Without including those in your identity program, you are only getting half of the information.
Cloud Security Best Practices That Are Already Table Stakes in 2026
Infrastructure as Code for Security Baselines
When the security posture of your cloud relies on people acting by the documentation, it will go out of track. This is addressed by Infrastructure as Code (IaC), which encodes the requirement to be more secure into the process of deploying.
Secure VPC/VNet templates. Hardened container base photos. Storage is automatically encrypted. Groups of network security that reject the incoming traffic unless it is explicitly permitted. They are not the manual checklists any more but are automatically deployed, version-controlled, and peer-reviewed.
The outcome is new environmental systems are provided with a safe foundation rather than being a blank page.
CSPM and CNAPP – Understanding the Difference
CSPM is a continuous scanner whether it is of misconfigurations, drift, or of gaps in compliance within your environment. It has become conventional several years ago.
Cloud-Native Application Protection Platforms (CNAPP) is more. By integrating posture control with workload protection, container security, CI/CD scanning and data exposure risk into a single prioritized view, they complement each other.
CSPM is usually sufficient when dealing with small settings. Organizations with multi-cloud or containerized workloads at scale should have CNAPP as a baseline, rather than an enhanced option. The experience that I received demonstrated that teams that were based on common CNAPP visibility might prioritize remediation in a much more precise manner than those that were correlating the result offered by four different tools.
Data Protection That Goes Beyond Encryption
Rests and transmissions of data must be encrypted. However, encryption does not provide you with knowledge of where your data is stored, who is able to read it and when it is going out of your environment as well.
That gap is filled with Data Security Posture Management (DSPM). It identifies and categorizes sensitive information found in the cloud storage, databases, and SaaS applications – and traces who accesses it and whether they should access it or not.
This coupled with Data Loss Prevention (DLP) and tokenization to high sensitivity fields gives the security teams the consonance it requires to control data risk proactively and not reactively.
What’s Just Starting to Shift And Why It Matters
AI as Both Shield and Attack Surface
CSPM, CNAPP, XDR and SIEM solutions now feature AI-based detection. They sift through the logs no human analyst could manage; detecting odd logins, odd data access, odd control plane activity – and automatically responding.
That’s the defensive side. The attack side is doubling up.
Cybercriminals are leveraging AI to produce more realistic phishing attacks, write self-evolving malware and, increasingly, prompt injection attacks on corporate AI systems. If your company has a chat-based AI assistant that has access to enterprise data, that’s an attack surface that most current models of security haven’t anticipated.
I’ve tested a couple of these new AI-powered SIEM platforms and the lateral movement detection is really impressive. But the problem is that the amount of alerts generated is high and without proper tuning, the signal will be lost.
Confidential Computing From Niche to Necessary
Encryption ensures data is secure at rest and in transit. Confidential computing protects data in use – while it’s being processed, in a Trusted Execution Environment (TEE).
This is critical for industries that are highly regulated (health, finance, government) and for multi-party workloads where multiple companies need to work with data while hiding it from each other. By 2026, confidential computing will be transitioning from a niche feature to become a mainstream offering by cloud providers.
Quantum-Safe Cryptography Is Already on the Roadmap
Post-quantum migration sounds distant. It isn’t. In 2024, NIST released its first batch of post-quantum cryptographic algorithms. The major cloud companies are starting to provide quantum-safe services. IT security professionals are being urged to plan for “crypto-agility” – being able to change cryptographic algorithms.
There’s no need to panic just yet. But if you’re designing systems today that will be in use five to seven years from now, you should be planning for quantum-resistant algorithms.
Where Most Organizations Actually Fail
The sophisticated threats get the headlines. The mundane attacks are the most destructive.
Public S3 buckets. Over-permissive IAM roles. Management ports exposed to the internet. Old resources left over from a project that shut down two years ago, but still running, unmonitored.
These are not rare. They are the norm in cloud security reviews across verticals and scales. In 2016 the problem won’t be that companies don’t know what to do – it’s that the pace of change will outpace manual processes.
This is worse with multi-cloud. There are different security models for different platforms. A security engineer who’s a star at AWS may not grasp the subtleties of Azure. Tool sprawl creates blind spots. Non-uniform logging formats make it difficult to get a single view. And then there’s the skills gap.
There’s still a huge shortage of security engineers skilled in cloud technologies. If they don’t have them, security gets tacked on retroactively – which is always more costly and less efficient.
For those interested in the bigger picture of protective tools, our round-up of the Best Cybersecurity Tools for Businesses in 2016 details how companies are addressing the tooling in this equation.
How to Actually Learn This Free Resources That Are Worth Your Time
Luckily, serious cloud security training is mostly free if you’re willing to look for it.
Cloud Security Alliance (CSA): Free PDFs of the Security Guidance, Cloud Controls Matrix (CCM) and CCSK body of knowledge. The CSA training site has free mini-courses on Zero Trust, DevSecOps, AI security and telemetry.
NIST and CISA: Free cloud security and Zero Trust maturity models and secure architecture patterns. NIST’s NICE catalog is an index of free cloud security labs, CTF challenges, and other resources on the internet.
Microsoft Learn (AZ-500 path): The free learning path “Secure cloud resources with Microsoft security technologies” goes in-depth on IAM, security of the platform, data and applications, and security operations. Similar paths can be found on AWS and GCP.
YouTube: Full AZ-500 course reviews, CNAPP reviews and cloud security architecture deep dives are available for free from the people who know them best.
How to learn: two to four weeks CSA guidance and vendor training modules, then four to six weeks experience – build something in a test environment, secure it according to best practice checklists, run a free CSPM tool against it and fix the issues. This far outweighs reading.
If you want to read more about cloud security in hardware and devices, you can read more in Cloud Security in Gadget Reviews for the consumer view.
A Practical Framework for Security Engineers and Developers
This is not an exhaustive list – it is an ordered list.
Start with identity. Lock down your IAM. Apply least-privilege rigorously. Include machine identities. Automate access reviews. This is the most important thing to prevent breaches.
Codify your baselines. Specify security in IaC. Create secure templates for common patterns like VPC/VNet setups, app stacks with WAF, private data platforms, so your organisation can re-use them.
Get posture visibility. Use CSPM at minimum. If you have containers or multi-cloud, consider CNAPP. Protect production and sensitive data paths, then prioritise a risk-based approach to remediation.
Shift left. IaC scans, container scans, dependency scans – all in CI/CD, with builds failing on critical issues. Fix security issues like other bugs.
Invest in logging and response. Centralize logs. Build MITRE-aligned detections. Conduct tabletop exercises and game days.
In my experience, the companies that were able to scale up security investment based on delivery impact (quick safe releases, lower risk of incident) were more successful than those that were focused on risk. You have to speak a team’s language if you want to change their behaviour.
My Take After Looking at This from Multiple Angles
The problem with cloud security in 2016 is the same problem. It’s the same problem (identity, configuration, data protection, visibility) at greater scale, with more attack surface, and faster-moving adversaries.
The companies that get it right aren’t always the ones that spend the most. They’re doing the fundamentals with discipline and rigour, they’ve automated wherever possible, and they’re taking a team approach to security, rather than a project approach.
The new technologies – CNAPP, DSPM, confidential computing, AI-based detection, post-quantum – are real and should be on your radar. But you don’t want to use them instead of the foundation.
If you’re starting from scratch, the CSA Security Guidance and your favourite cloud provider’s free online security training are a good place to start. If you’re more advanced, the most important thing you can do is catch up on what you’ve learned.
Read:
How to Improve Website Security Before Someone Else Does It For You
ICR Apps for Identity Verification: How Businesses Improve Security and Compliance
I’m a technology writer with a passion for AI and digital marketing. I create engaging and useful content that bridges the gap between complex technology concepts and digital technologies. My writing makes the process easy and curious. and encourage participation I continue to research innovation and technology. Let’s connect and talk technology!